Not only hackers can use keyloggers to intercept your keystrokes to extract passwords and other sensitive information.
After reading enough articles about cybersecurity and hackers, you will definitely stumble upon a topic about keyloggers. Sounds very sinister, mysterious and technological, but what are keyloggers in fact and how dangerous are they?
Well, in this article, we will tell you everything you need to know about them. What it is? How are they used? How to detect keyloggers? And how can you protect yourself from them?
What are keyloggers?
Keyloggers (also known as keystrokes) are programs that bind themselves to your operating system or web browser. As the name suggests, their purpose is to remember keystrokes on your device.
They can be programmed to remember everything you type or type only on certain sites and fields (such as the PayPal password field). Therefore, keyloggers are usually considered malware.
Most often, they get on your device along with virus software, although they are not viruses themselves. Sometimes they can even be legally used (but that doesn’t make their use ethical).
How do keyloggers work?
Let’s explain in a simple way.
When you use the keyboard, your keystrokes are transferred from it to your device. Your keyboard driver translates the scan code (keystroke data) into letters, numbers, and symbols. Through this process, your operating system and any application you use can recognize your presses.
So, the keylogger pretends to be the receiving device, and thus receives click data in the same way as the operating system or applications you use.
Software and hardware keyloggers
Most people are only familiar with software keyloggers – programs designed to remember keystrokes that run in the background of your operating system.
Usually, those who install a keylogger on your device block access to it and the data it collects. They can also configure the program to send the collected data via e-mail, websites or upload to databases.
Hardware keyloggers also exist. These are physical devices that perform the same functions (remember keystrokes). But they don’t need to be installed, instead you physically connect them to your computer.
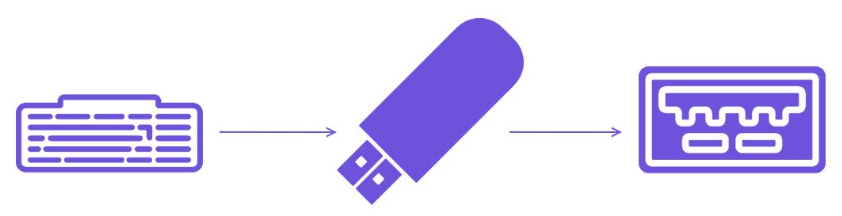
Most hardware keyloggers are installed in a USB port, through which the wire from the keyboard must be connected to the computer. Right in between, to be exact.
That is, instead of this:
This happens:
If you don’t know what a hardware keylogger looks like, here’s an example:
Yes, you can easily buy it on Amazon or even Aliexpress.
Why would anyone use hardware keyloggers?
The biggest plus of such keyloggers is that the software cannot detect them. In addition, they do not depend on software, so software errors do not affect their operation.
In older models, the person using the keylogger had to extract it in order to access the data stored on it. But newer models can connect to a local WiFi network and send data via email.
Hardware keyloggers are still used if the victim is the owner of a desktop computer. However, in the case of a laptop, it will not be difficult to detect such a keylogger.
Oh yeah, and don’t think you’re immune to a hardware keylogger if you’re using a wireless keyboard. Many of them are vulnerable to KeySniffer attacks. Although not a hardware keylogger, it also allows an attacker to obtain keystroke data if they are transmitted over an unencrypted communication channel.
In addition, there is also KeySweeper, a hidden hardware keylogger that looks like a regular charger. It can passively monitor, decode and remember keystrokes from various wireless keyboards. Next, it sends keystroke data to the attacker via GSM. Moreover, you can configure it to send data based on:
- custom names
- URL links
- Keywords
How are keyloggers used?
For cyberattacks, right? Yes, hackers use keyloggers very often. But they are not the only ones who do this. Surprisingly, families and internet marketers can use them too.
hackers
Keyloggers are a useful tool for cyber criminals. Often, this is how they manage to hack into user accounts and get corporate data. Hackers usually distribute keyloggers via:
- Trigger installations or activations when you click on a link or open an attachment in a phishing email.
- Launching the installation or activation of a specific program.
- Use of other malicious programs (in particular, Trojans) to install keyloggers on the device.
- Using vulnerable browsers with web page scripts.
- Creating fake websites and using phishing messages or MITM attacks to interact with them.
In some cases, cybercriminals can even set up a keylogger in such a way that it enters the network and spreads to all devices connected to it. Or they may set up other malicious software to be installed from that network. Hackers can also install hardware keyloggers in Internet cafes. Or a scammer may steal valuable information about the business in which he got a job.
And no, seasoned cybercriminals aren’t the only ones using keyloggers. Even failed mommy hackers who are in school can use keyloggers to boost their grades.
Famous cyber attacks using keyloggers:
- In 2015, hackers used phishing and keyloggers to break into the servers of the insurance company Anthem.
- In 2016, researchers at RisklQ (in collaboration with CleaeSky) discovered that cybercriminals were using a web keylogger to hack many popular eCommerce sites.
- In 2016, security researchers at Trend Micro discovered that hackers used a commercial keylogger program (Olympic Vision) to hack employee and executive accounts in 18 countries (USA, Middle East, Asia).
- In 2018, a new strain of malware called Virobot was discovered. It could not only perform the functions of a keylogger, but also ransomware and botnet programs.
- In 2017, hackers used keylogger malware to break into the San Antonio Women’s Health Institute, San Antonio’s largest gynecological institute.
Employers
Companies often use keyloggers to track their employees. This is called “corporate keylogging" and it is absolutely legal, at least as long as keyloggers are only installed inside the corporate network and only on work computers.
Employers usually use software keyloggers. IT teams can set them up to detect keywords and send real-time alerts when someone copies files, enters sensitive data, or executes hidden commands.
Within the company, it makes sense to use keyloggers:
- This helps security services find insider threats.
- This helps managers and supervisors to ensure that employees meet the required performance indicators and do not let them relax.
- It also helps auditors verify that the business is complying with laws and regulations. If someone inside the company violates them, then keyloggers will help to easily identify this person.
Do all employers use keyloggers? There is no exact information about this. We think it’s safer to assume that your management installed keyloggers on company computers than to simply hope not. Read your entire lease agreement. There may be an item about logging keystrokes.
But in any case, if you can work from your personal computer, then bringing it to work should be safe.
Internet marketers
Back in 2017, researchers at Princeton University found that roughly 482 of Alexa’s top 50,000 websites (quite popular websites) were using web scripts that acted like keyloggers. And scripts remember not only keystrokes, but also mouse movements and scrolling.
Why should they do it? Because it helps marketers collect behavioral data about you. How exactly do you interact with their sites, which ads interest you the most, what content do you like and dislike, and so on. In addition, IT teams, product managers and/or business owners, UX designers can also use keyloggers to identify and implement user wishes, usually during an unboarding or beta release.
Sounds doubtful? Yes, but generally legal as they mention it in the user agreement. You know, that long page of text and legal clauses that you’re too bored to read (don’t worry, most people do).
And to be honest, it makes sense. This greatly helps companies make the user experience more personalized.
Jealous spouses and overprotective parents
Husbands or wives who are concerned that their significant other is cheating on them, or parents who want to keep a close eye on what their kids are doing online can also use keyloggers.
No, we are not exaggerating. There are even articles on the Internet that recommend the best keyloggers to monitor children’s social media activity.
Is it legal? It is hard to say. The use of keyloggers is illegal in most countries. However, according to some divorce lawyer websites, using them can be technically legal if you’re "careful". Also, the article we linked to above says that you can use a keylogger if it is installed on your device. This gives the impression that parents can do this (if their children do not have receipts to prove that they bought the devices).
We will tell you how to detect a keylogger and get rid of it in the second part of this article, which will be released very soon!