North Korean hacker group BeagleBoyz started robbing banks via remote access again from February 2020 in order to fund the North Korean regime
North Korean hackers known as the BeagleBoyz are using malicious remote access tools to steal millions from international banks, according to a report released today by several US government agencies.
The report states that the North Korean hacker group BeagleBoyz has again started robbing banks via remote access since February 2020 in order to fund the North Korean regime.
Hackers steal money using Santander ATM bug
The bug allowed attackers to use fake debit cards to withdraw more funds from ATMs than was on the balance.
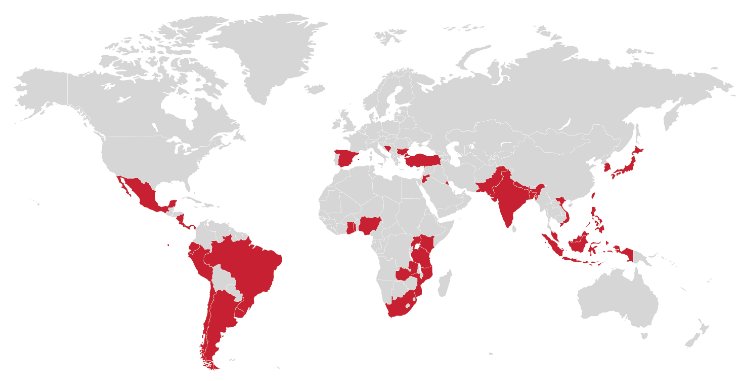
The BeatleBoys are currently attacking banks in over 30 countries around the world as part of an ongoing bank robbery scheme in an attempt to steal $2 billion, US Cyber Command tweeted.
Countries attacked by the group
“Since February 2020, North Korea has resumed targeted work with banks in many countries to initiate fraudulent international money transfers and cash withdrawals from ATMs. The recent recovery follows a lull in bank targeting since the end of 2019.
In one attack on ATMs, BeagleBoyz hackers managed to withdraw cash from ATMs operated by banks in dozens of countries, including the United States.
For example, they managed to steal $81 million from Bangladesh Bank in 2016. Fortunately, the Federal Reserve Bank of New York was able to stop the $1 billion transfer attempt after detecting anomalies in transfer instructions received from the Bank of Bangladesh.
Hackers showed how to force popular ATMs to issue money and customer data
Researchers have introduced two new zero-day vulnerabilities in popular ATMs that allow them to obtain bank customer data, as well as make the ATM “spit money".
The BeagleBoyz are part of the North Korean government’s General Intelligence Bureau and have been active since at least 2014, stealing hundreds of millions from banks to finance the country’s regime.
BeagleBoyz overlaps with other groups monitored by cybersecurity companies, including APT38 (FireEye), Bluenoroff (Kaspersky), Lazarus Group (ESTSecurity), and Stardust Chollima (CrowdStrike).
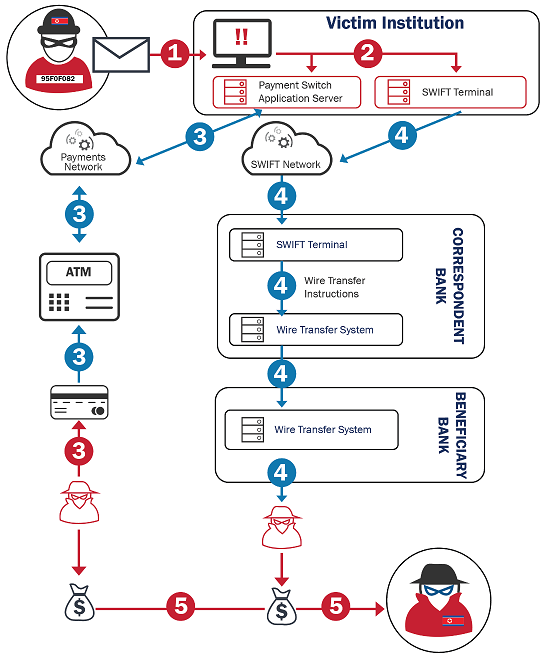
Scheme of the BeagleBoyz attack
BeagleBoyz uses a variety of tools and methods to gain access to a financial institution’s network, study the topology to discover key systems, and monetize their access. The technical analysis above is an amalgamation of many known incidents, not the details of a single operation,” the agencies said.
North Koreans have been observed using a wide range of methods to gain access to victims’ systems, including various forms of phishing as well as social engineering, from 2018 to early 2020.
They may also have used the services of criminal hacking groups such as TA505 to initially gain access to targeted financial institutions, and several months later, in some cases, carried out a final attack on victim bank systems.
“In addition to robbing traditional financial institutions, the BeagleBoyz targeted crypto exchanges to steal large amounts of cryptocurrencies, sometimes valued at hundreds of millions of dollars in a single incident,” the advisory concluded.