The FCC has released new photos of the outside and inside of the GrayKey iPhone unlock device.
For the past couple of years, a startup has been selling a device to police and intelligence agencies that can unlock an iPhone, although it has been shrouded in mystery until now.
Some details about how the device, called the GrayKey , works, and which agencies use it, have slowly been leaked to the media. But until today, only two images of the GrayKey device have been widely circulated. One was included in a Wall Street Journal article in 2018 and another was published by security company MalwareBytes in the same year.
Now, more photos have surfaced after GrayShift, the device’s makers, filed a series of documents with the FCC as part of an application for an FCC ID, a process all tech products in the US must go through to ensure they comply with FCC standards.
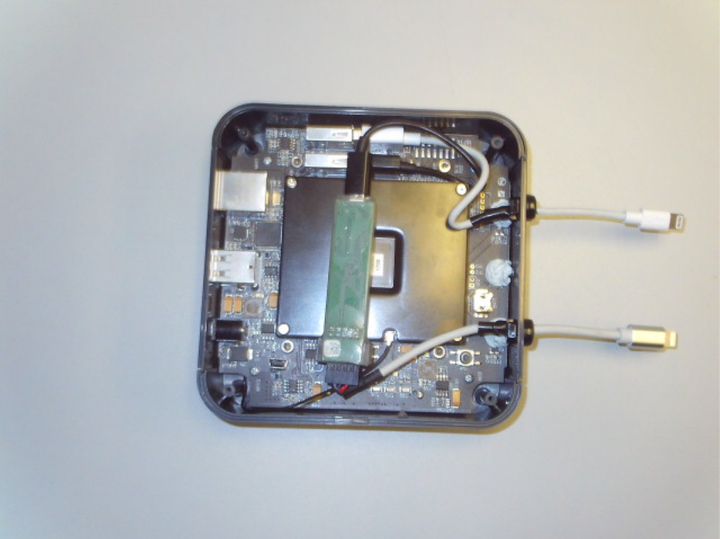
Motherboard was able to take a look at these photos and get a rough idea of what’s inside.
The documents include photographs of the GrayKey’s internals, which show it is built on an ARM processor, manufactured by Compulab.
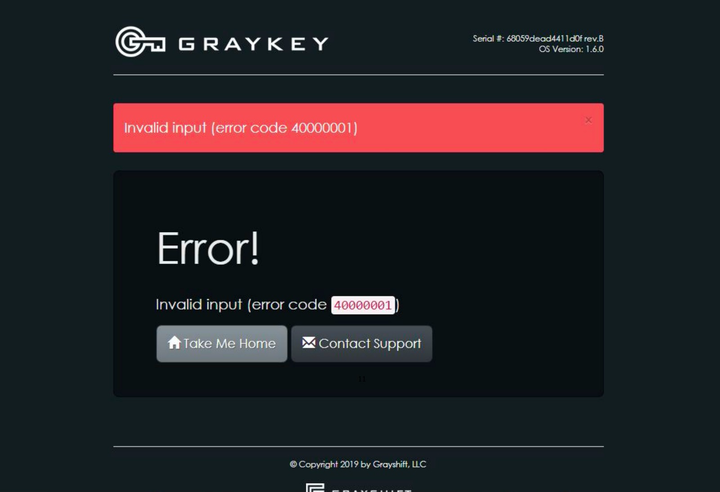
Separately from the photos released by the FCC, Motherboard obtained a screenshot of the user interface of the GrayKey device through a request for public records from the Providence Police Department. A screenshot was attached to the GrayKey email as part of the bug report.
In March, Motherboard published an article on more than 500 cases where authorities have tried to access iPhones with varying degrees of success. In some of these cases, the agencies used the GrayKey to locate the phone. However, the authorities also encountered common problems repeatedly, such as a password that was too long or an unlock option not available for that particular model at the time.
GrayShift and Apple regularly outdo each other, with GrayShift finding ways to bypass iPhone security and Apple introducing new protections to stop them. In 2018, Apple introduced a limited USB mode, which was mentioned in leaked GrayShift messages previously received by Motherboard. This feature essentially sets a narrower time limit in which a law enforcement officer can unlock a device.
These new images are unlikely to mark a major shift in this game of cat and mouse, but will at least finally give the public a more accurate idea of the device that is usually hidden away in forensics labs.