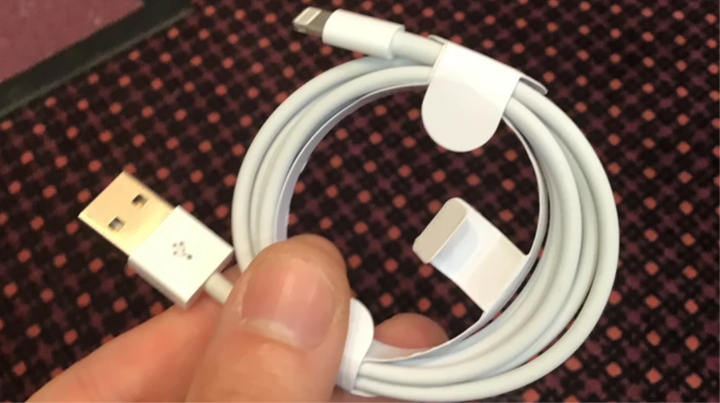
It looks like an Apple Lightning cable and works like an Apple cable, but gives an attacker the ability to remotely connect to your device.
Most people don’t think twice before taking a phone charging cable and plugging it in. A security researcher has shown how USB cables, even those that look exactly like an Apple Lightning cable, can hijack your device.
I connected the Apple Lightning cable to my iPod and then plugged it into my Mac as usual. My iPod started charging, iTunes detected the device, and a pop-up appeared on my iPod asking if I want to trust this computer. Nothing suspicious.
But this cable hid a secret. Some time later, a hacker remotely opened a terminal on my Mac screen and was able to execute any command on my computer. This is all because it was not an ordinary cable. It was modified to include an implant – additional components placed inside the cable, allowing a hacker to remotely connect to a computer.
The hacker, alias MG, took an innocent-looking Apple USB Lightning cable and fitted it with a small Wi-Fi-enabled implant that, when connected to a computer, allows a nearby hacker to run commands as if they were sitting right in front of the screen.
Image: MOTHERBOARD.
Dubbed the O.MG cable, it looks and functions almost indistinguishably from an iPhone charging cable. All the attacker has to do is replace the live cable with a malicious one and wait for the target to plug it into their computer. From a nearby device and within Wi-Fi range (or connected to a nearby Wi-Fi network), an attacker can execute commands on a computer over the wireless network, or trigger predefined commands to execute.
“It looks like a real cable and works exactly the same. Even your computer won’t notice the difference. Until I, as an attacker, take control of the cable wirelessly," said the security researcher known as MG, who made these cables. He demonstrated how it works at the annual Def Con hacker conference.
Once connected, the attacker can remotely control the infected computer, for example, to send realistic phishing pages to the victim’s screen, or remotely lock the computer’s screen to obtain the user’s password upon re-login.
What is inside this tiny USB cable, you ask, to make it capable of such attacks? That’s the trick: inside the housing of the USB "A" connector is a circuit board loaded with a WiFi microcontroller (documentation doesn’t specify which one) that will send the payload through the USB device.
Think of it like a BadUSB device, like the USB Rubber Ducky, but which looks exactly like the original cable from Apple. This is the best way to log in and all you have to do is plug in a USB cable to your computer.
Future updates to this cable may include a port for ESPloitV2, an open source Wi-Fi controlled USB HID keyboard emulator. This will give more power to this device, which already has tremendous capabilities.
The cable comes with various scripts and commands that an attacker can run on the victim’s machine. A hacker can also remotely "kill" a USB implant to hide evidence of its existence.
In the video below, you can see the hacker executing code remotely using an O.MG cable connected to a MacBook.
MG focused its first attempt on the Apple Lightning, however its implant can be used with just about any cable and against most target computers.
“This custom Lightning cable allows for cross-platform attacks, and the implant I created is easily adaptable to other types of USB cables,” MG said. "Apple is just the hardest to implant, so it was a good proof of my capabilities."
Similar cables for Lightning, Micro USB, and USB Type C are now available for purchase, and prices start at $120.
In his day-to-day work as a RedTeam specialist at Verizon Media, he develops innovative hacking techniques and techniques to identify and fix security vulnerabilities before attackers discover them. While this is a personal project, MG said developing it could help red teams think about protecting against these types of threats.
These days, most people know not to plug unverified flash drives into their computer, but they don’t expect the cable to be a threat either.
MG has spent thousands of dollars and countless hours working on his project. It took him about four hours to assemble each cable. He also worked with several other hackers to write some of the code and develop exploits.