The vulnerability has already been reported to Microsoft before, but they consider it a "feature".
Custom Windows 10 themes can be used in "Pass-the-Hash" attacks to steal Windows credentials from unsuspecting users.
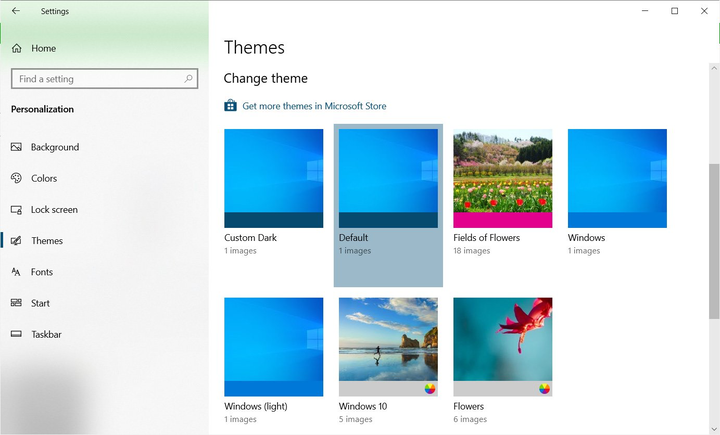
Windows allows users to create custom themes containing custom colors, sounds, mouse cursors, and wallpapers that the operating system will use. After that, Windows users can switch between different themes at will to change the look and feel of the operating system.
The theme settings are saved in a folder % AppData% Microsoft Windows Themesas a file with a .theme extension, such as Custom Dark.theme.
Windows themes can then be shared with other users by right-clicking the active theme and choosing "Save theme for sharing", which will package the theme into a file.deskthemepack.
These theme packs can then be emailed or downloaded to a website and installed by double-clicking on the file.
Custom themes can be used to steal Windows passwords
This weekend, security researcher Jimmy Bain discovered that user-created Windows themes can be used to perform a Pass-the-Hash attack.
Pass-the-Hash attacks are used to steal Windows usernames and password hashes by tricking the user into gaining access to a remote SMB share that requires authentication.
When you try to access a remote resource, Windows will automatically attempt to log in to the remote system by sending the Windows login username and an NTLM hash of its password.
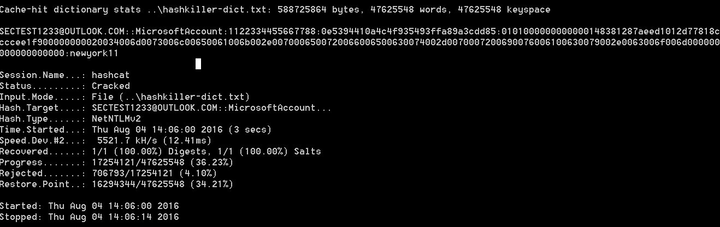
In a Pass-the-Hash attack, the submitted credentials are collected by the attackers, who then decrypt the password and obtain the username of the visitor.
In a test previously conducted by BleepingComputer, it took about 4 seconds to crack a simple password.
Cracking an NTLM password in four seconds
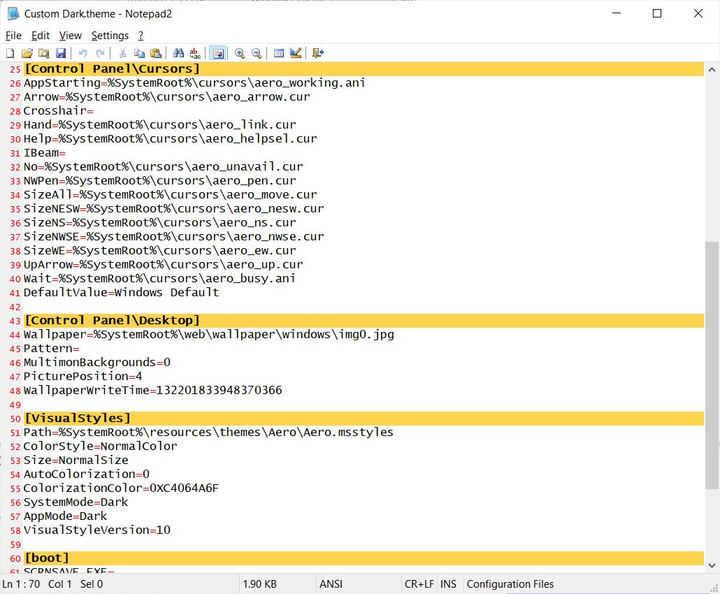
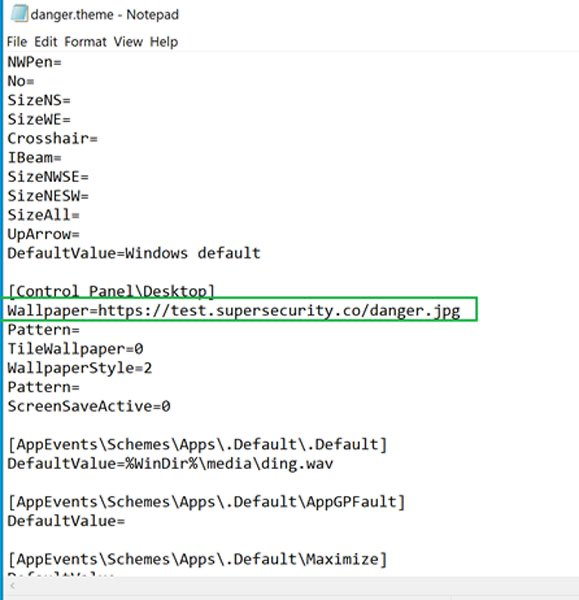
An attacker can create a custom .theme file and change the desktop wallpaper setting to use a resource that requires remote authentication, as shown below.
Malicious Windows Theme File Source: Jimmy Bain
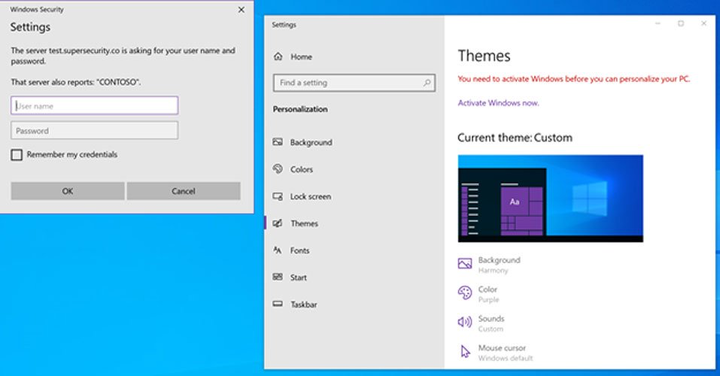
When Windows tries to access a resource that requires remote authentication, it will automatically attempt to log into the share by sending an NTLM hash and login to the account.
Automatic login attempt
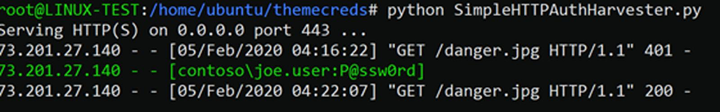
The attacker can then collect the credentials and decrypt the password using special scripts.
Collecting Windows Credentials Source: Jimmy Bain
Because the Pass-the-Hash attack allows the account used to log into Windows, including a Microsoft account, to be stolen, this type of attack becomes more problematic.
As Microsoft moves from local Windows 10 accounts to Microsoft accounts, remote attackers can use this attack to more easily access the many remote services offered by Microsoft.
This includes the ability to remotely access email, Azure, or corporate networks.
Bain stated that he reported the attack to Microsoft earlier this year, but was told it would not be fixed, as it was "a feature by design."
Protection against malicious theme files
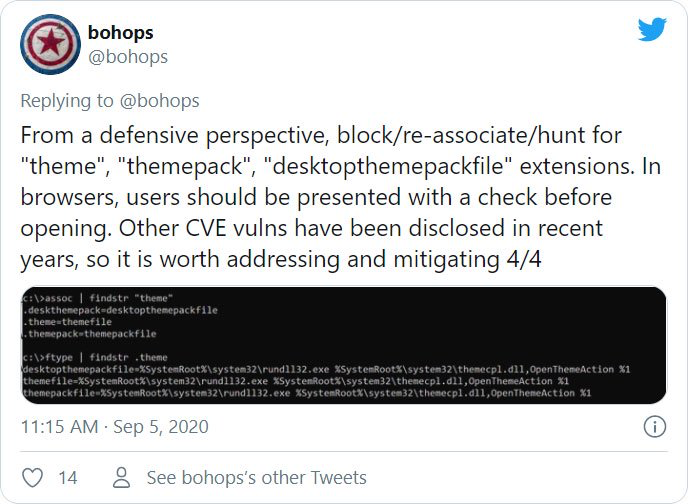
To protect against malicious theme files, Bain advised everyone to block or re-link extensions .theme, .themepackand .desktopthemepackfilewith another program.
However, this will break the Windows 10 Themes feature, so only use this tip if you don’t need to switch to a different theme in the future.
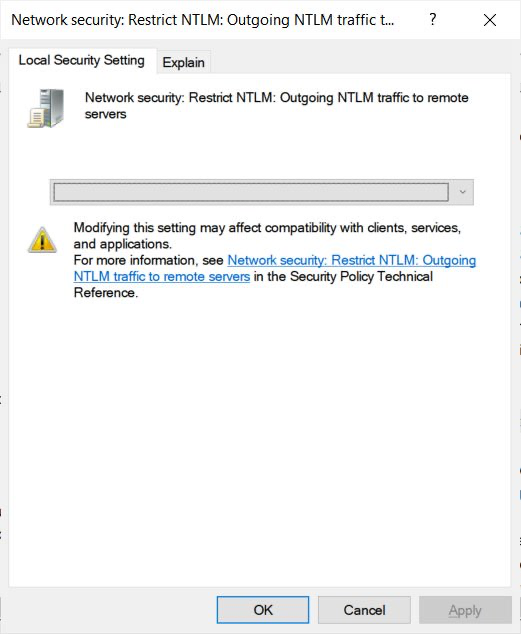
Windows users can also configure a group policy called Network Security: Restrict NTLM: Outgoing NTLM traffic to remote servers and set it to Deny all to prevent your NTLM credentials from being sent to remote hosts.
Restrict NTLM: Outgoing NTLM traffic to remote servers
Note that configuring this setting may cause problems in corporate environments that use remote shares.
We also recommend enabling two-factor authentication on your Microsoft accounts to prevent attackers from remotely accessing them, even if they have successfully stolen your credentials.