Malicious software can disable notifications from security systems integrated into devices.
Starting with a little-known piece of malware, security researchers at ESET have uncovered new Android spyware distributed through fake messaging apps like Threema, Telegram and WeMessage.
The malware comes from APT-C-23, a group of experienced hackers who have been running spy campaigns against military and educational institutions since July 2015.
The updated version, discovered earlier this year, shows off an impressive array of new features that, among other things, allow spyware to dismiss notifications from security systems running on Samsung, Xiaomi and Huawei devices and thus be able to run without being detected.
Hiding in fake apps
In April 2020, MalwareHunterTeam security researchers tweeted about Android spyware having a very low detection rate on VirusTotal. After examining the sample, ESET researchers found that it was part of a malware suite used by APT-C-23 attackers.
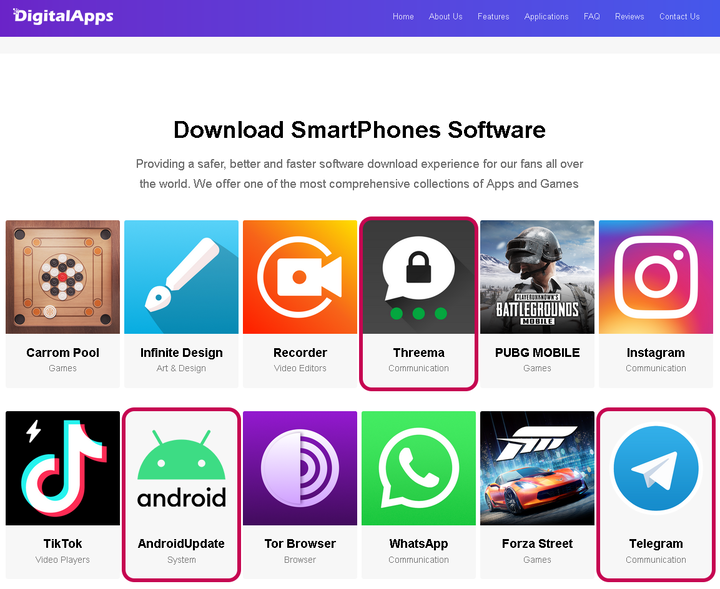
About two months later, in June, the MalwareHunterTeam discovered a new sample of the same malware hidden in the Telegram messenger installation file available from DigitalApps, an unofficial Android app store.
Since their security solution was one of the few that managed to detect the new spyware from APT-C-23 in the public domain, ESET launched an investigation and it turned out that the malware was also hidden in other applications in the aforementioned store.
They also found it on Threema, a secure messaging platform, and AndroidUpdate, an app that is a system update for the mobile platform.
With the help of Threema and Telegram, the victim will get the full functionality of these applications along with malware, thus hiding the malicious nature of fake applications.
Perhaps in an attempt to control the spread of malware, the attackers added a fake download gateway, requiring a six-digit code.
ESET believes that the DigitalApps store is just one of the distribution methods that the attackers used to infect victims, as they found other applications that were not available in the store but contained the same spyware.
“In June 2020, ESET systems blocked this spyware on client devices in Israel. Malware samples detected were disguised as WeMessage messaging app, says ESET
However, the GUI of the malicious application differs from the original and appears to have been created by an attacker, indicating that it did not attempt to impersonate a real product.
Improved feature set
APT-C-23s are known by various names (Big Bang APT, Two-tailed Scorpion) by other cybersecurity companies. The group deploys malware for Windows (KasperAgent, Micropsia) and Android (GnatSpy, Vamp, FrozenCell) platforms, targeting targets in the Middle East.
Compared to previous Android spyware, the latest version of APT-C-23 expands functionality beyond the already present capabilities of audio recording, stealing call logs, SMS, contacts and certain file types (PDF, DOC, DOCX, PPT, PPTX, XLS, XLSX, TXT, JPG, JPEG, PNG).
The list of features now includes the ability to disable notifications from security apps integrated with devices from Samsung, Xiaomi and Huawei, allowing malware to remain hidden even if its activity is detected.
In addition, the software can now read notifications from messaging apps (WhatsApp, Facebook, Telegram, Instagram, Skype, Messenger, Viber), effectively stealing incoming messages and account access codes.
Spyware can also record the screen (video and image) as well as incoming and outgoing calls through WhatsApp. It can also covertly make calls by creating a black screen that mimics an inactive phone.
ESET has published a technical report detailing the new features of the APT-C-23 Enhanced Spyware, which contains useful indicators to help you recognize a compromised device.